In the modern era, various mobile devices play a significant role in contributing towards organizations' success. One of the main challenge with exotechnology is with securing corporate data.
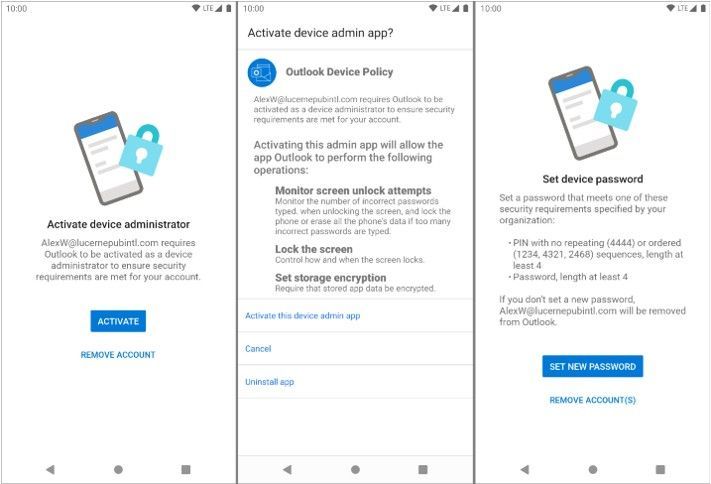
I was assisting a user today with adding his Android device to our MDM system (Microsoft Intune), and he came across the message "Activate Outlook as Device Administrator App," which probably all of us have undoubtedly seen and handled.
Just like any other organization, we also deploy mobile devices as both business owned and Bring Your Own Devices with a combination of iOS and Android, and host mailboxes on Microsoft Exchange.
Also, it is a legitimate question for the end user to wonder why the Outlook software needs to be added as the device administrator on his own Android smartphone. And why is this required? I was able to convince him of its necessity and significance, which made me wonder: Why not spread the word to everyone so that everyone is aware of what the Device Admin App is and why it is necessary? So, let's get going, then!
Android 2.2 was the first version of Android to support managing mobile devices. Enterprise requirements have changed since then. Devices are being used in a wider range of use cases and accessing more private resources than the original device admin API for Android was intended for. Some examples of these use cases are:
It doesn't support several enterprise use cases because a device admin can be activated by any program for which the user grants permission. Examples include:
Since Android 5.0 introduced device owner and work profile modes, device administration has been seen as an outdated technique. With the release of Android 9.0, Google has been removing a few policies to make Android Enterprise more secure. Few policies that are deprecated now:
USES_POLICY_DISABLE_CAMERA
USES_POLICY_DISABLE_KEYGUARD_FEATURES
USES_POLICY_EXPIRE_PASSWORD
USES_POLICY_LIMIT_PASSWORD
We now know about "Device Administration", so let's understand why it is needed.
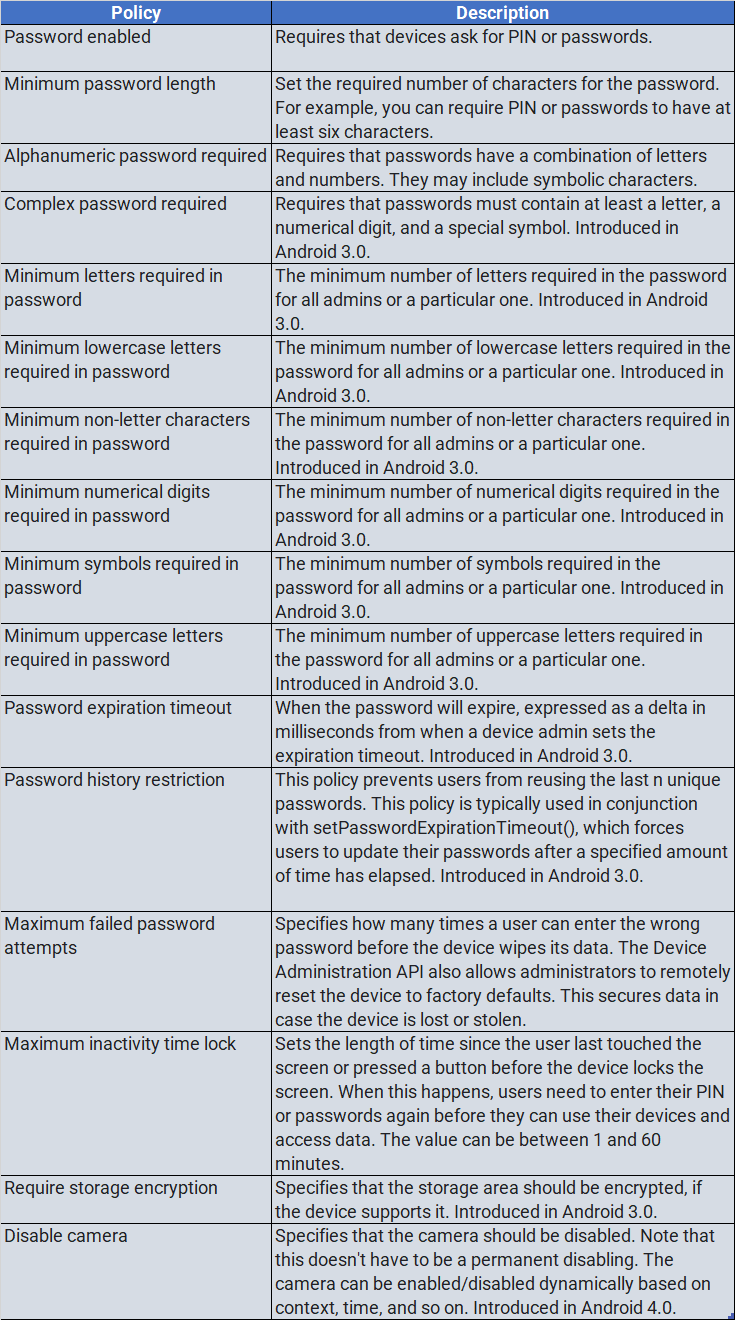
Enterprise apps need support from the underlying operating system to implement or enforce device administration features, which require access to specific APIs at the system level. Using these APIs, app developers can enable the app to be "security-aware"; that is, the app knows that it has to behave/work in an enterprise context and at the same time, it helps the enterprise control corporate devices. For example, the native Android email app leverages these APIs to support Exchange policies. IT administrators can use the email app to enforce password policies — including alphanumeric passwords or numeric PINs — across devices. Administrators can also remotely wipe on lost or stolen handsets.
Few apps that use the Device Administrator APIs:
Let's know understand how these app(s) that have access to device admin APIs can control the device features:
If the user denies activating the app as device admin app, then it will not enforce it's policies and the app remains on the device as in-active app.
It depends on the actions configured in the app as to what it should do in the event of non-compliance when the app is deployed and the dependent policies are enforced.
In most cases, a user is denied from accessing corporate resources if their device is evaluated to be non-compliant with the security policies in place. In a nutshell, if a device (for example, a legacy device) does not support all of the stated policies, there is no way to allow the device to connect.
The strictest policy is enforced if a device contains multiple enabled admin apps. There is no way to target a particular admin app. Users must first unregister the app as an administrator to remove an existing device admin app.
Device Administration API currently only supports passwords for screen lock.
In the modern era there is a variety of mobile devices that play a great role in contributing towards organizations success. One of the main challenge with exotechnology is with securing corporate data. An end user accesses corporate data from all type of devices like personal, corporate or kiosks and for each type of device there exists a policy for securing the data.
Coming back to Android devices, usage of device admin configuration depends upon the management type of your device:
An EMM deploys a work profile to create an OS-level container that separates a user's personal and work data and programs on their devices. The option to deploy applications utilizing managed Google Play gives businesses greater assurance that data won't be unintentionally or knowingly shared with unapproved applications. Furthermore, if a person leaves the company, IT administrators have the ability to selectively delete enterprise data without affecting their private files.
An EMM has full lifecycle management over the Android device and its data when a managed device is enrolled as fully managed.
Lockdown of hardware features, defense against factory reset and unenrollment, administrative remote wipe and reset of the entire device, and customization of programs with support for kiosk or single application deployments are all included in this. The three deployment modes listed below are often administered by organizations utilizing managed device mode, though these can be combined throughout an organization's fleet depending on its needs:
Here is an excerpt from the Device Administration sample manifest:
override fun onPreferenceChange(preference: Preference, newValue: Any): Boolean {
if (super.onPreferenceChange(preference, newValue)) return true
val value = newValue as Boolean
if (preference == enableCheckbox) {
if (value != adminActive) {
if (value) {
// Launch the activity to have the user enable our admin.
val intent = Intent(DevicePolicyManager.ACTION_ADD_DEVICE_ADMIN).apply {
putExtra(DevicePolicyManager.EXTRA_DEVICE_ADMIN, deviceAdminSample)
putExtra(DevicePolicyManager.EXTRA_ADD_EXPLANATION,
activity.getString(R.string.add_admin_extra_app_text))
}
startActivityForResult(intent, REQUEST_CODE_ENABLE_ADMIN)
// return false - don't update checkbox until we're really active
return false
} else {
dpm.removeActiveAdmin(deviceAdminSample)
enableDeviceCapabilitiesArea(false)
adminActive = false
}
}
} else if (preference == disableCameraCheckbox) {
dpm.setCameraDisabled(deviceAdminSample, value)
}
return true
}Device Administration is an old way to get Admin access for your App and access features which otherwise is not available, like getting failed login notification, change pin and lock screen. It used to be difficult to uninstall an app on an Android phone with device admin enabled, but with newer Android versions, it's simpler because the user will receive a popup instructing him to turn off the program's admin privileges.
Use the most recent Android Management APIs if you want to make it very tough to uninstall the app. The organization controls the app, and only has the authority to unlock it for uninstallation. This is typically utilized by companies who give their staff mobile devices and have stringent regulations requiring that they install a certain number of apps.
Thank you for staying with me on this topic. Would be looking out for your sugestions. 😃