Background This post is once again focused on macOS devices since, over the past few days, there have been discussions in various communities about installing the Cisco AnyConnect VPN solution on business-owned macOS machines. So, I thought of sharing my own experience of deploying the VPN solution with no user
This post is once again focused on macOS devices since, over the past few days, there have been discussions in various communities about installing the Cisco AnyConnect VPN solution on business-owned macOS machines. So, I thought of sharing my own experience of deploying the VPN solution with no user interaction required and, at the same time, securing it 2FA. Reason for 2FA – Ensure that users can only connect to this VPN solution from a corporate device, as anyone can easily download & connect the VPN client from their personal devices.
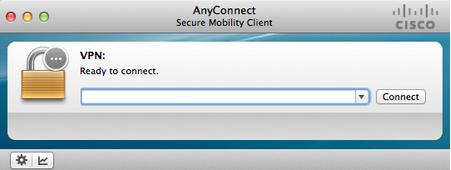
Like any other VPN solution, the Cisco AnyConnect VPN allows you to connect to the corporate network allowing access to specific allowed resources and services as if you are on the corporate network.
Deploying AnyConnect involves silently installing, configuring, and upgrading the AnyConnect client and its related files on end user’s devices:
The Cisco AnyConnect Secure Mobility Client can be deployed remotely to devices by the following methods:
You can include optional modules that enable supplemental features, client profiles that set up the VPN, and optional features when you deploy AnyConnect.
As we are focused on Intune as an enterprise device management system, in this article, we will focus on the first approach of deployment, i.e. “Predeploy”.
To start with, you need to have access to the following:
AnyConnect uses a network system extension on macOS 11 (and later), bundled into an application named Cisco AnyConnect Socket Filter. The AnyConnect extension has the following three components that are visible in the macOS System Preferences-Network UI window:
AnyConnect requires its system extension and all its components to be active for proper operation, which implies that the mentioned components are all present and show as green (running) in the left pane of the macOS Network UI.
For installation in the system context, macOS requires the extension to be approved via MDM without end-user interaction.
To approve the AnyConnect system extension without end-user interaction, we need to push the system extension payload to the devices using Intune. To do so, follow these steps:


This is how the configuration profile should look like:

Sadly, there isn’t a way to accomplish this via the online UI of Microsoft Intune. You must first build an XML configuration and then upload it as a configuration profile. To do so, please follow the steps:


Or, you can copy-paste and save this as XML to upload to the profile:

As a next step, we will create the required profile for the VPN client and will push it to the devices as a shell script.
Shell Script for profile:
!/bin/sh
mkdir -p /opt/cisco/anyconnect/profile
cat <
EOF
When it comes to iOS/macOS devices, I prefer to push the corporate apps as LOB apps as it gives more control over the app.
P.S – The feature is in public preview
The following prerequisites must be met before a macOS DMG app is installed on macOS devices.
Follow the steps to push the VPN client to the devices:

Alright, so by now, you have deployed the VPN app and configured all the required settings so that the app gets installed without any user interaction.
Now, as the last part of this post, let’s control the configuration so that the connection can only be initiated from a corporate device.
And to achieve this, you need to define specific parameters in the Cisco ISE platform that ensures that the device initiating the connection is a corporate device. There are numerous ways of doing it; you just need to make sure that the parameter you define is unique and cannot be modified at the device level.
An example of configuration:
So, when the user initiates the VPN connection, the device will be evaluated first and once passed, only then will it be allowed to access corporate resources.
You can easily deploy the Cisco Anyconnect VPN client to your corporate macOS devices.
I’d love to know what you think, so do leave your comments below, and if you liked it, then do share it.
Cheers/
Somesh